

| Current | v9 | v8 | v7 | v6 | v5 | v4 | v3 | v2 | v1 | All | About |
MW6 Technologies QRCode ActiveX 3.0
In this section the previously provided information will be demonstrated with the help of a recent public ActiveX vulnerability and exploit. The vulnerable control is from a company called WM6 and comes with their ``QRCode ActiveX'' version 3.0. When I downloaded the software in January 2008, several months after the exploit was posted on Milw0rm in September, the vulnerable control was still part of the package.
The control itself has a CLSID of 3BB56637-651D-4D1D-AFA4-C0506F57EAF8. After the installation of the software, it can be found in the registry in:
HKEY_CLASSES_ROOT\CLSID\{3BB56637-651D-4D1D-AFA4-C0506F57EAF8}.
The DLL that implements this control can be found on the harddrive in the file that is specified in the "InprocServer32" key. In this example it is:
C:\WINDOWS\system32\MW6QRC~1.DLL
A screenshot of what the entire registry entry for this control looks like:
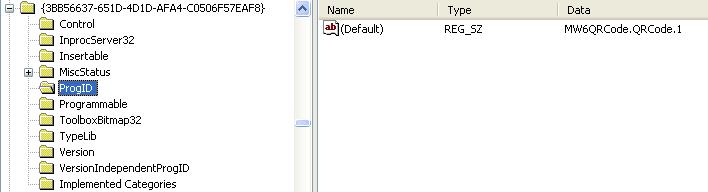
There are two interesting things to note here. For one, the ProgID key has
a default value of MW6QRCode.QRCode.1. At the ProgID's corresponding location
in the registry, namely HKCR\MW6QRCode.QRCode.1, the CLSID subkey
contains the CLSID of that control. This tells us that this control can be
instantiated using both its CLSID and ProgID. Another point of interest in
the screenshot is the absence of the "Implemented Categories" key. This means
that this control is neither part of the "safe for scripting" nor the "safe
for initialization" category. However, it appears that the control must
implement IObjectSafety since it is still possible to instantiate the
control from IE. The following simple HTML code tries to instantiate the
control.
<body> <object classid='clsid:3BB56637-651D-4D1D-AFA4-C0506F57EAF8' id='test'> </object> </body>
The result of this snippet of code is the appearance of a little picture in IE. As this works just fine without Internet Explorer complaining about being unable to load the control, the next examination step is in order.
Subsections