| Current | v9 | v8 | v7 | v6 | v5 | v4 | v3 | v2 | v1 | All | About |
Message Format
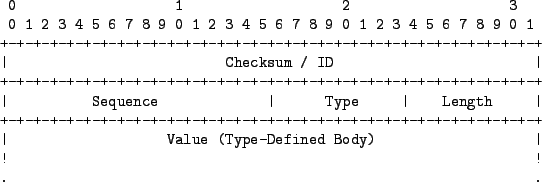
The format of the messages that the SteganRTP applications use to communicate with each other is described in the following sections. Figure ![[*]](8/3/images/html/crossref.png) below describes the core message format of all types of SteganRTP formatted messages. This format consists of two fields, the Checksum / ID and Sequence fields followed by a standard Type-Length-Value[25] (TLV) structure. The Checksum / ID, Sequence, Type, and Length fields comprise the message header, while the Value field is considered the message body, or payload.
below describes the core message format of all types of SteganRTP formatted messages. This format consists of two fields, the Checksum / ID and Sequence fields followed by a standard Type-Length-Value[25] (TLV) structure. The Checksum / ID, Sequence, Type, and Length fields comprise the message header, while the Value field is considered the message body, or payload.
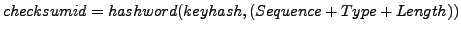
The 32-bit Checksum / ID field contains a hash value which is used to identify whether or not a potential message that is extracted from the payload of an inbound RTP packet is indeed a valid SteganRTP communication protocol message. The hashword[26] function is used to compute this hash. The function's two primary operands consist of the keying information defined as keyhash in Section ![[*]](8/3/images/html/crossref.png) and the sum of the message's Sequence, Type, and Length header fields. This value is defined as checksumid and is described by Equation
and the sum of the message's Sequence, Type, and Length header fields. This value is defined as checksumid and is described by Equation ![[*]](8/3/images/html/crossref.png) below.
below.
The verification of extracted potential messages is required due to the fact that some packets in the inbound RTP stream may not contain SteganRTP messages if there was no outbound data waiting to be sent by the remote application when the RTP packet in question traversed it. The hash function used to compute this checksum value incorporates the keyhash so as not to be computable solely from message data, which would allow an observer to also verify that a message is embedded within the RTP payload.
The 16-bit Sequence field is a standard incrementing sequence number, the 8-bit Type field indicates what type of message it is, and the 8-bit Length field indicates the length, in bytes, of the Value field. The Value field contains the message's payload.