| Current | v9 | v8 | v7 | v6 | v5 | v4 | v3 | v2 | v1 | All | About |
Initialization
Upon start-up, SteganRTP first initializes various memory structures such as message caches, configuration settings, and an RTP session context structure.
The most notable task performed during the initialization phase is the computation of keying information used by various components. The method chosen for creation of this keying information is to create a 20-byte SHA-1[21] hash of a user-supplied shared secret text string. Due to the result of this operation being used as keying information by various components of the overall SteganRTP system, this shared secret must be provided to both SteganRTP applications that wish to communicate with each other.
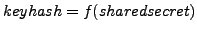
The 20-byte result of the SHA-1 hash function against the user-supplied shared secret is defined here as the keyhash and described by Equation ![[*]](8/3/images/html/crossref.png) below where f represents the SHA-1 hash function.
below where f represents the SHA-1 hash function.
Subsections